 Pirates session
Pirates session
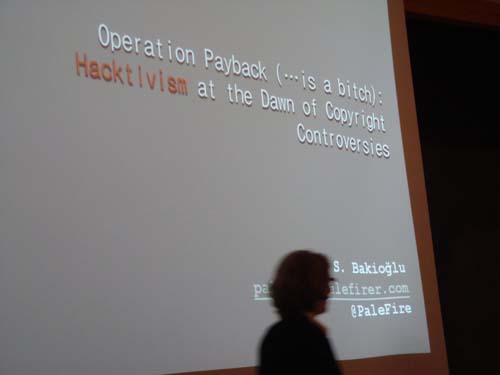
Burcu Bakioglu, Operation Payback (…is a Bitch): Hacktivism at the dawn of Copyright Controversies
Bodo Balasz, Informal Media Economies – What Can We Learn from the Pirates of Yesteryear?
Martin Fredriksson, The Ideology of Piracy and the Public Spheres of Modernity
Jinying Li, Piracy, Circulation, and Cultural Control in Cyber-Age China
moderator: Marcienne Martin
Unfortunately I was able to attend only the talk by Bakioglu.
- culture of piracy is what they call copypasta [or copy paste]. It is a subversive culture. Response to it was to extend regulation and limitation of piracy.
- The ‘culture’ perceived any copyright issues as a threat to creativity, to corruption exposure, privacy, an act of criminalization of society, surveillance.
- They were a true networked society that was lateral: hoizontal modes of communication presenting alternative strategies of resistance.
- Sites of struggle: The Pirate Bay. This alternative form of protest took the form of hacktivism. It is non-violent civil disobedience [DDOS attacks, site defacements etc.]
- It used to be a sub-culture but now it is becoming mainstream.
- Wikileaks and Assange are a model. Nodes that exchange information and give power. One therefore needs to intercept flow of information and leak it out.
- Op Payback began when an Indian company was contracted and announced it would take down Pirate Bay [co. called aiplex.com].
- Case of ACS Law solicitors whose site was taken down and in effort to remedy problem hurriedly put their site back up and inadvertently published secret information that stayed online for two hours and the info proved it was damaging enough to the company because it exposed its illegal dealings.